RICOH RansomCare powered by BullWall
The problem with relying on 100% prevention, 100% of the time
We might as well face the facts: Ransomware is getting smarter and even the most well-protected organisations fall victim to attacks.
With ransomware attacks increasing each year it’s getting even more important for public and private organisations to prepare themselves for tomorrow, not for yesterday.
The solution
RICOH RansomCare powered by BullWall is an agentless solution that monitors activity on file- and cloud shares. As soon as the solution detects ongoing criminal encryption and file corruption, it triggers a response to isolate and disable the compromised device while encrypting your data. It is the critical extra layer of your defence strategy when other security solutions fail.
Features & Benefits
RICOH RansomCare powered by BullWall is a quick and simple way to protect your company against ransomware attacks.
- Detect – Detailed live visibility with paybackAll activity is displayed on a dashboard in real-time. You can witness the near-immediate response to any attack as it happens
- React – Stop attacks within secondsThe solution will react within seconds of any unexpected file encryption taking place. It will also notify those who need to know.
- Respond – Keep your business running smoothlyThe speed of response allows Ricoh’s containment solution to prevent the spread of the attack beyond a single user – keeping things business as usual.
- Recovers – Take the pressure off your operational teamAn exact list is compiled of the few affected files before the single user’s forced shutdown, making it easier to recover documents.
Watch the Live Demo of RICOH RansomCare powered by BullWall
Shut down ransomware before it spreads
In this eBook, you’ll learn:
- The difference between perimeter-based defences vs detect and contain
- Why containment solutions are the most effective response to stop an attack
- How to stay protected with RICOH RansomCare
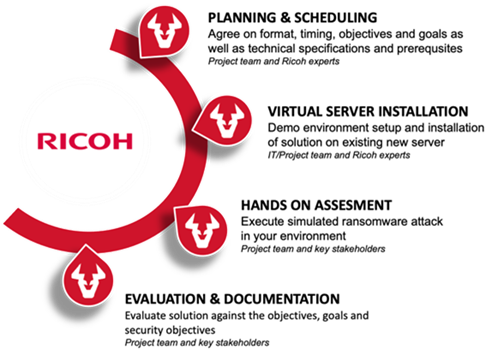
Easy to implement
Our containment solutions can take as little as four hours to be installed and can usually be done remotely - meaning minimal disruption to your team and business.
Before installation you can try-out a risk-free demo presentation too.
Why choose RICOH RansomCare powered by BullWall
RICOH RansomCare protects your organisation from the ever-increasing prevalence and sophistication of ransomware attacks. As the additional layer of protection, it complements your existing security defences and provides total peace of mind.
- Immediate response and endpoint isolation when ransomware activity is detected
- Low IT overhead with agentless solution enabling fast and easy remote deployment
- Detailed reporting simplifies data restoration and compliance reporting
- Complementary layer to the security defence already running

break-line















